Something Smells Phi-shy
I was going to talk about password manager, but I have been running into more and more phishing emails while working. I then realized that we are now in the era of cyberpunk. To quote the famous line from the "Hackers Manifesto."
" This is our world now... the world of the electron and the switch, the beauty of the baud. "
Looking at the SolarWinds and Microsoft Exchange hack, we can see now that criminals and nation-states are moving away from the physical world and going into the digital world.
You shouldn't only rely upon big tech companies to protect from cybercriminals. There is only so much that Google and the other big five can do to protect you. Moving forward, I want to go over the ways criminals try to get your information. Let's start with Phishing emails.
What is a Phishing email?:
Phishing is when a cybercriminal sends an email that looks to be sent by a reliable source to trick you into sending passwords, credit card numbers, and other PII (Personal Identifiable Information).
One technique used is for a cybercriminal to send an incorrect URL sent as a shortened URL that will redirect you to a download page that will have malware. Another trick is to have a fake page with a keylogger (a program that can track the inputs from your keyboard) to get your passwords and usernames.
How do I protect myself?
There are some simple ways to protect yourself from phishing attacks.
1. Use two-factor authentification. All websites in their settings have the option of setting up 2FA. I would suggest against using SMS because SMS text can easily be bypassed. Authenticator apps and Yubikey are safer options. This will make it so even if your passwords are discovered, they will need physical access to your phone or yubikey.
You and your Yuibikey — Alex's infosec journey (atphinn.com)
2. Update. Update Update. Whenever Windows or Mac tells you there is an update, please do it. Yes, it is annoying, but what is more annoying is dealing with identity theft. Apple updates are usually aways when a vulnerability is found. Windows have a patch Tuesday, the second Tuesday of the month.
3. If you receive an email or chat with a link, hover over the link to confirm if it goes to the actual website. It is safer to go to the site directly and not click the link in the email.
4. Check for misspellings and grammatical errors. I can confirm that big companies have people who specifically write client/customer-facing texts and check multiple times for spelling and grammar errors.
What do I do if I receive a phishing email?
If you receive a phishing email at work, notify your IT/Security team, even if you are unsure. Their motto is better safe than sorry. I was at a company that got hit with Ransomware from phishing, and we were down for a month, and that was a lot of sleepless nights that the IT team has. They instead have a red herring than a month-long fix.
In your personal life, the same thing applies. Even if it looks somewhat suspicious, report it. Gmail, apple mail, Outlook all have a report spam button in their toolbar and block the email address.
Currently, this is how cybercriminals and scam artists work. They send a text, email, or call to trick you into giving you PII. By doing the above, you will be able to protect yourself.
You and your Yuibikey
Happy new year to everyone. I think this is the best time to review our internet security, especially after the SolarWinds hack, which showed that anyone, including the government, can fall victim to hacks.
SolarWinds, How did it happen?
The Solar Winds hack was not a one-day operation. The APT group had access to the Solarwinds system since 2018. They were able to gain access due to weak passwords, and then move around connected apps to access different companies.
Lesson learned...Don't use weak easy to guess passwords. The first thing to do is set up a password manager like Keepass, which will generate strong passwords and save your login for you to auto-fill it at a later date.
This is not the only thing that we should do to secure our accounts. We need to enable two-factor authentication (2FA).
What is 2FA?
Two-factor authentication is using alongside a strong password, having another system to authenticate our login.
Some examples of 2FA are:
Authentification apps (Like Google Authenticator)
Text messages (We won't go over since it is easy to get around)
Email(Same Above)
Biometrics (Using fingerprint or Face)
Yubi Keys
This article will go over Yubi Keys, as they are considered one of the best forms of 2FA.
A Yubi what now?
A Yubi Key is a hardware device generally in the form of a USB drive that allows you to access multiple services like websites, computers, or networks. The Yubi key has a cryptographic algorithm software that will enable users to securely login to their accounts. Using this Algorithm is generates a robust and unique passcode to a service or program you are using.
What makes this safer than many of the above examples is that someone will need physical access to the Yubikey to use it. Text messages and email are weak because criminals have ways of spoofing your email and text messages so that the one-time passcode is sent to them.
Ok, how do I get one of these magical Keys?
You can go to Yubico.com to purchase a key. There are several versions of the Yubikey. I bought the Yubi key 5, which has NFC, so I can unlock my phone.
Setup is simple but is Unique to each service, Normally you will have to go into your account settings to an app or website like amazon. And choose the setup 2FA option. You can use the below site to see how to set up 2FA for multiple locations.
You can use this site to find a way to set up 2FA; Two Factor Auth.
You can also use the Yubi key site to set up your Key for specific websites.
How to Setup the YubiKey | Yubico
I am not going to explain how to set this up as it is self-explanatory on the above sites.
Next, we will talk about Password managers. I will also start security-focused IG, and I am thinking of posting some of the hacking challenges.
Shut your Pi-hole!!
In this article, we are going to build a pie-hole, which is relatively easy and will make you feel like an l337 hacker.
Pi-Hole?
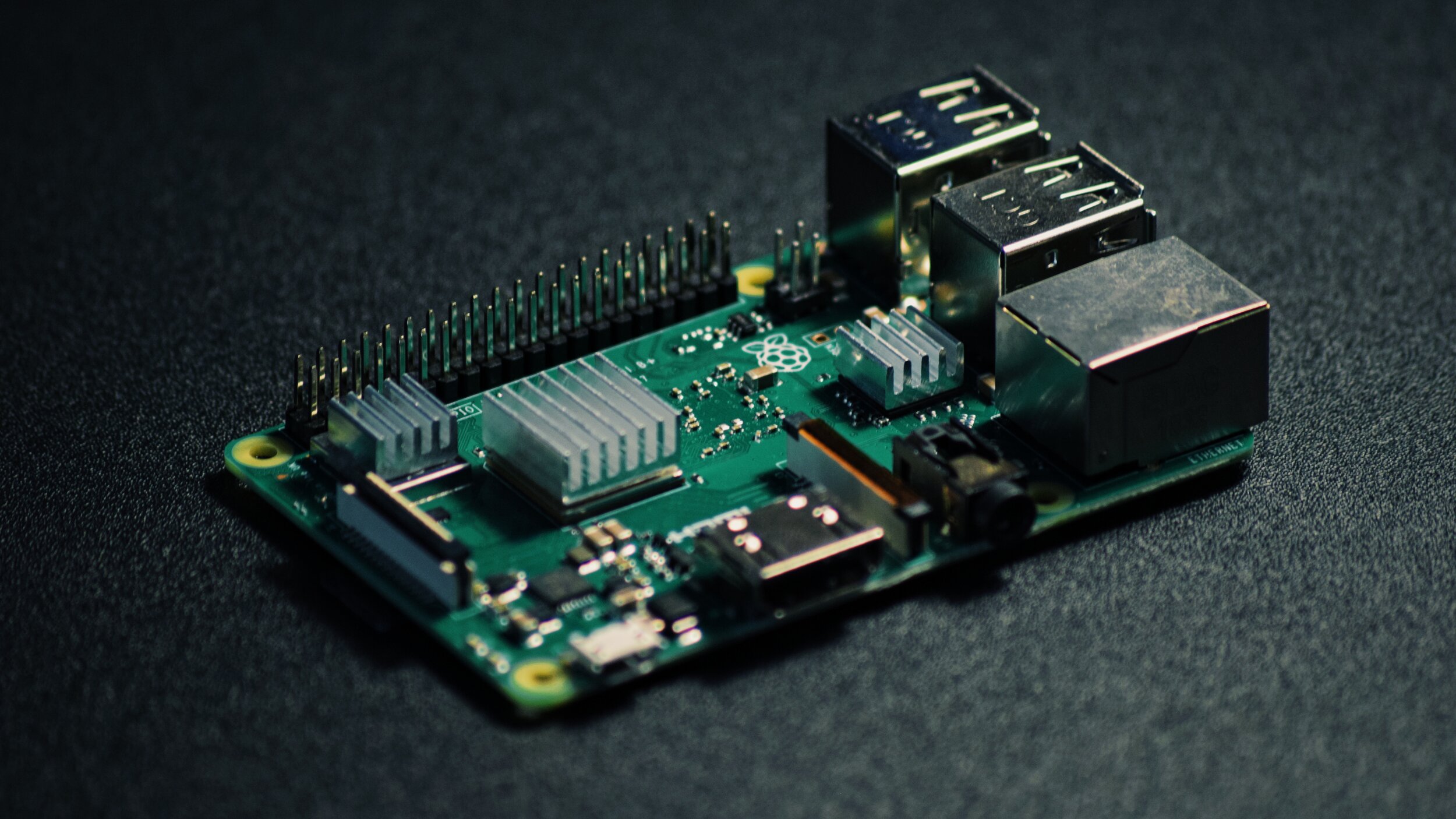
Raspberry Pi
Before we explain what a Pi-hole is, let us talk about what a raspberry pi is. A raspberry pi is a mini motherboard that inventors use to prototype invention ideas that they have, for example, cell phones.
A Pi-hole is a raspberry pi that has software added installed that will block ads at the network level. Referencing my previous blog:
https://www.atphinn.com/blog/the-best-trick-to-troubleshooting
The Network level is where data transferred through your router to the Web.
Having the Pi set to this means that any computer that joins your local network (LAN) with automatically have an ad-blocker implemented.
Now to preference, advertising on the internet is not inherently a bad thing. It does keep small sites and small businesses, articles, etc. up and running.
But there is also the danger of adware being downloaded to your computer via online ads.
What is adware?
Adware is "any software that installs itself on your system without your knowledge and displays advertisements when the user browses the Internet," aka another form of malware.
Adware is how a lot of the scams that tell you "your computer is hacked call Microsoft" are performed.
But my browser has an ad blocker installed. Why would I use a Pi-hole?
While installing an ad blocker on your browser is easier, here are the reasons I prefer a pi-hole:
It is an open-sourced technology, so your data is less likely being sold, there are rumblings of browser adblockers having advertisers pay to "stop" their ads from being blocked.
I don't have to install an ad blocker on every device that you buy, once they join my LAN that instantly have ad block enabled
For parents, you can control what sites to block. Not only with they have to find a way to get past the router and Pi-hole settings.
It adds another layer of network security by blocking malicious domains and people using google hacking to find open ports.
Finally, of course, the joy of building something that you own and have control over.
I'm sold; let's build a Pie-hole.
What you will need to build this is:
Raspberry Pi (https://www.raspberrypi.org/products/raspberry-pi-4-model-b/) 2-4gb is fine
Ethernet cable
16 GB sd card
Setting up the pi-hole
Open the pi, and with it should come with an already formatted SD card with Linux raspbian.
If there isn't a pre-made sd card, you can download the image here: https://www.raspberrypi.org/downloads/raspbian/
Download Etcher to flash the raspbian OS on to the SD card, by just selecting the ISO and SD card. https://www.balena.io/etcher/
Unmount by right-clicking the sd card and selecting eject
Now we are going to do this the less tech-savvy way cause it is easier.
Insert the SD card into the PI and connect it via HDMI to a monitor, connect it directly into your wireless router and attach a keyboard and mouse, then plug it in.
The great thing about Raspbian version of Linux is that it is super user friendly, follow the prompts to set a password (strong one)
Once done, open the menu and select the terminal.
Here is the L337 hacker part, in terminal paste the following command: curl -sSL https://install.pi-hole.net | bash, Hit enter
It will download and run the script that will set up the Pi-hole.
The first screen tells you that you are about to transform your Raspberry Pi into a network-wide ad blocker. Hit enter
Click ok at the donate screen to move forward, and the next screen is informing you that you must have a static IP address. The good thing is that it will do this for you; Hit enter.
Next, you will have to pick a DNS server for ease of use, select Google because you want to ensure that you will have access to websites. If they go down, then there is a severe issue.
The next screen is third party lists that the pi-hole references to block domains, keep the defaults. Hit enter
I would also Hit enter in the select protocols to be safe. To see more information about protocols see my previous blog: https://www.atphinn.com/blog/the-best-trick-to-troubleshooting
You will then see your network settings the top number is your IP address, copy this down. The second number is your router IP
In the next few prompts, you can hit enter.
You will reach an Installation Complete window. Note the URL and password that is generated. We are done with the pi, and you can disconnect it from the screen, keyboard, and mouse.
Finally navigate to you router and find the DNS settings. This is normally under advance settings. Add the pihole IP address that we copied to static DNS field. You will the be finished.
You can go to your main computer and type the URL into the browser. You should see the Dashboard—login with the password from before.
Next time we will go over the Dashboard.
Pealing the Onion with TOR.
We are going to continue off from the last post about VPNs and talk about the TOR browser and network.
Wait, what is TOR?
TOR stands for The Onion Router, and it is a software/browser that enables you to browse the web anonymously. The onion part of the name comes from the layers of protection that the browser uses to hide your internet browsing session.
Like I mentioned before, engineers like their puns.
How does it work?
Tor, similar to a VPN, bounces your connection through a global volunteer overlay network to conceal your location. A large company that may sell your data does not own this network; anyone can own one of these networks, even you.
This is how it can hide your internet activity by going through a number of these networks.
This sounds too good to be true, what is the catch?
One thing that you will sacrifice is your speed since your data will be moving through multiple networks around the world.
TOR is another way to access different content for a website like Netflix. The only issue is that you don't have control over your location. You will have to refresh your connection to get the right place. From my experience, it is more reliable to get around the access restrictions of sites like Netflix.
How do I get started with TOR?
First, download the TOR browser: https://www.torproject.org/download/
Install the TOR browser and run it
Click the shield icon, and you can use this to set the level of security you want. The highest level will break some sites and cause them not to work.
The wand icon is where you can adjust your location. You can click it to keep refreshing till
Think of TOR as another browser you can use. Firefox helped develop this browser and have incorporated some of the technology in the Firefox browser.
And the Deepweb/Darkweb?
You can access the Deep/Dark web with the TOR browser and a specialized search engine. Instead of .com or .net domain, the Dark web sites use the unique .onion domain.
I HIGHLY RECOMMEND NOT TO TRY TO ACCESS THE DEEP WEB, AS YOU WILL PUT YOUR COMPUTER AT RISK!!!
The Dark/Deep Web, in a nutshell, is indexed websites that are either old or have almost not traffic sent to it. So these sites are then ignored by most modern search engines. From experience, there isn't anything on the dark web that you can't find on the normal (also called Clear web), or they are old Geosites webpages.
You can host a web site on the Darkweb, but hackers will continuously attack you there.
That is it about TOR, next, we will go over what a PI HOLE is and how it block ads!
VPNs What? why? where?
There has been an increase in the articles about VPNs and how great they are for web browsing and that VPNs protect your data, making it harder to collect your data.
We are also told that we can bypass the region rules set by specific apps, for example, Netflix to see shows that we don't have in our country of origin.
But how does that work?
What is a VPN?
VPN or Virtual Private network takes a private network and allows a user to access it even when they are connected to a public network.
For example, if you are at Starbucks using the Wi-Fi, you will be able to access your private network, IE, your router/modem.
You can confirm this by first connecting to the Starbucks Wi-Fi without your VPN. Then do a google search what my IP. You will see your current IP address. Let us assume that you have a VPN to your home network.
When you turn on the VPN on your computer, check again, and your IP will change to your home network's external-facing IP address.
For a majority of VPNs, they use encryption to protect your data by obfuscation via a tunneling protocol. The encryption is done as the data moves down the OSI model mentioned in a previous post, and it gets encrypted at each step.
https://www.atphinn.com/blog/the-best-trick-to-troubleshooting
In essence, it works as follows:
You browse to a site
Your computer with a VPN then will make a call to your private network with your access credentials
The network validates your credentials sent by the VPN.
You are correct and allows you access to the private network.
The private network then makes a call through the internet for the website.
That data is then sent back to your computer for you to see the website
Why use a VPN?
For a regular user using a VPN can be used to access region-locked sites since most VPNs have networks across the world. You can access them via their apps. These "private networks" to tell websites that you are in another country.
It would help if you used a VPN when you are connected to a public network, like hotel wifi. When you are using the hotel wifi, your information is being sent without any protection—making it easy for a malicious actor to collect and read your data while you are browsing the web. As mention previously, with a VPN, your information is encrypted, making it harder to read.
For Corporations, VPNs are used for protection of data, but also allows users to access files that are hosted in a corporate network located in a different location.
They are a lot of VPNs, how do I choose?
VPNs are an excellent way to add a layer of security to your browsing session. When picking a VPN, I look for ones that don't keep logs. So if it is compromised, there is almost no data available.
Below is a list of VPNs that I used.
https://the-bestvpn.com/vpns-do-not-keep-logs/
Unfortunately, not many free VPNs remove these logs, BUT there is an open-source program called TOR that some believe hides your identity and data better than any VPN.
But we will go over Tor in the next article.
Use Google like a Dork!
Today we are going to hack google…..well, not really. What we are actually doing is using the built-in search filtering of Google, Bing, and other search engines.
How does a web search engine work?
A search engine is a program that takes in a word or phrase that you input and then scans the internet for websites, images, and documents that have keywords that match. It then lists the results on the webpage.
This scanning process is also known as crawling, because the program that is scanning is called a spider.
Engineers like puns. Get it a spider crawling the World Wide Web.
What is Google Dorks?
Google Dorking/ Google Hacking is a technique the uses phases called operators to look for specific information on the internet.
Below is the Wikipedia site that has a list of the operators.
https://en.wikipedia.org/wiki/Google_hacking
Lets get to dorking
In this example, We are looking for documentation about a Tp-link Archer router. Below is the initial search.
We get a large number of results returned in our search.
A good start, but we do not want to spend time clicking through the site to find our documents. So let us narrow the search a bit with the operators inurl: and filetype:
Nice we are no down to 366 and the search finished quicker 0.12 seconds. Looking further down the page we have a direct link to the pdf we want to download for the 3rd choice (You always want the latest documentation). Easy!!
The reason that this was faster is because we gave the search engine a specific set of parameters to look for. Telling it to skip urls that don’t match the inurl: parameter and are not PDF documents (filetype:).
I use this most of the time to find documents for devices I have where I threw them out or if the Ikea instructions are missing.
Why should you worry about this?
Like all things hacking, there is a dark side. Google Dorking is how some scam artist gets their information about their targets. Imagine if someone searches for a resume. Now they can get a personal email address or even guess a work email to send malicious emails.
They can even use this to find IoT devices like a nest with weak security protocols to hack into.
https://www.hackread.com/printers-hacked-to-promote-pewdiepie-youtube-channel/
Even some companies have gotten hacked from theses techniques. Because hackers found "hidden" login pages with weak/default passwords to get into their websites and databases.
https://www.welivesecurity.com/2018/02/22/unsecured-amazon-s3-buckets-expose-private-data/
Knowledge is power. Use that power to keep yourself safe.
The best trick to troubleshooting
Please do not throw sausage Pizza away!
No, you did not read the above wrong; this is an acronym that IT teams use to troubleshoot issues with your computer and your network connections.
How does Sausage Pizza relate to Information security? This acronym helps to remember the layers of the OSI model for step by step troubleshooting.
How would I use this??!!!
The OSI model can be used as a step by step checklist to troubleshoot computer or internet connection issues that you have. Once you know where the problem lies, you can now understand what to fix with the help of some Google-Fu.
OSI, Layers, what?
OSI, which translates to The Open Systems Interconnection model, is a reference guide that was developed in 1978 by Hubert Zimmermann to help teach computer networking concepts on how data moves between the seven networking layers.
So what does the acronym stand for?
Please (Physical), Do (data), Not (network), Throw (transport), Sausage (Session), Pizza (Presentation), Away (Application)
Physical - This consists of printers, computers, ethernet cables, printer cables, modems, etc.
Data - Represents the information that is transferred between devices; for example, a document you send to the printer.
Network - Represents how the data in your home move between your devices. Your modem/router uses your IP address is used as an identifier to know where to send data. Think of it as how UPS knows where to deliver your package, and your IP address is your street address.
Transportation - Is the data that is sent to outside of your network, for example, when you type in a website address into your browser that millisecond it takes to load is this layer in action. Internet speed test function at this layer when checking your speed
Session - Manages the flow of the data between computers and networks; this is the internet, a bunch of networks connected.
Presentation - This layer deciphers the data so that the next layer in the OSI model can translate it. I like to think of this layer as a projector, and it converts the stills of the film to a full-motion movie.
Application - This is the screen that moviegoers view the film on. This layer takes all that data that is sent back and forth between layers 4, 5, and 6, makes it viewable for us the user. Web browsers, Netflix, and email clients like Outlook are all listed on the Application level.
In this example, the HTML code in the red box becomes the site above.
Here is a recent example of how I used OSI.
A friend of mine was having trouble accessing the internet.
The first thing I did to troubleshoot was to make sure the modem and router was connected the modem connected, and the wiring was attached correctly(Physical).
Next, we checked that the computer was communicating with the router (Data). You can do this by going to your routers admin page, as I mentioned in my first blog. If you can connect, then everything is fine (Data/Network).
This is when we found out what the issue was. The issue was that the computer kept disconnecting from the router when we were in a different room, but when we were in the same room as the router we did not see any issue with connection to the router. From there, I was able to deduce that the layout of the apartment was affecting their Wi-Fi signal.
At this point, I suggested that they get a Wi-Fi extender to amplify the signal. Quick, easy, and no need to call your cable company
Now I have to build that Wi-Fi extender. But that is a separate blog.
In summary the OSI model is helpful because it gives use a check list to of issues that can cause your devices to have connection problems. This will eliminate the need to contact your telecommunication provider with unnecessary back and forth conversations.
Secure your phone before you protest!
In light of current events, this post is to protect the information on your phone if things escalate at a peaceful protest.
Before I go on, I am not a lawyer, and I would highly suggest you read up on your right to privacy.
Why should you protect and secure your smartphone?
The current climate as it is in America, if you go out to protest, and you are filming law enforcement, there is a chance that they will try to take your phone and force you to unlock it without a warrant and use that information against you. Unfortunately, if you have your fingerprint scanner or face recognition activated on your phone, law enforcement is allowed to use your fingerprint or face to unlock your phone.
https://www.buzzfeednews.com/article/jasonleopold/george-floyd-police-brutality-protests-government
https://www.documentcloud.org/documents/6935297-LEOPOLD-DEA-Memo-George-Floyd-Protests.html
These tips will not only protect your privacy but will also help with general smartphone security.
Securing your phone!!
1. Disable all biometric unlock for your phone. As mentioned before, the law doesn't protect you from the Police forcefully using your fingerprint or face to unlock your phone. Also, hackers have found ways to bypass the fingerprint scanner.
If you do a quick search, several sites show how to bypass the fingerprint scanner. Apple switched to the face scanner in hopes of better security, but that too was shown to be insecure.
Using passcode and patterns, however, are harder break into, and would require direct access to the phone to break the encryption, even then some phones by default wipe a phone after several failed attempts.
Passwords/passcodes both fall under the 5th amendment, so you are not legally obliged to tell law enforcement your pin or pattern. Also, Make sure that your phone is set to auto-lock after a few minutes.
2. Disable lock screen notifications. This tip is self-explanatory. You do not want your messages that may be private to viewed without your authorization, so it is best to turn this off.
3. Turn on Airplane mode. Airplane mode turns off all of your phone's radio signals like Wi-Fi, Bluetooth, NFC. Making you harder to track by law enforcement.
There is a tool called a StingRay that law enforcement uses to track the cell phone signals of suspected criminals, and now they are using it against black lives matter protesters. So it is a good idea to use airplane mode while you are out protesting.
https://techcrunch.com/2020/05/27/aclu-ice-stingray-documents/
4. Use Signal as your messaging app. Signal is an open-sourced messaging app that has end to end encryption.
End to end encryption at a high level means that only the two users that are communicating can read the messages that they are sending to one another. This also prevents potential eavesdroppers like your telecom / Internet provider from reading your messages.
With Signal, you can also permanently delete your messages from your history.
Signal: https://www.signal.org/
Andriod: https://play.google.com/store/apps/details?id=org.thoughtcrime.securesms&hl=en
IOS: https://apps.apple.com/us/app/signal-private-messenger/id874139669
5. If you are worried that if you go to a protest that your phone will get taken, use a burner phone and leave your main phone at home. You can use a cheap flip phone with a pre-paid sim card for this.
Please DO NOT turn it on while at home, that will negate the purpose of having a burner phone, because once you turn this phone on, your location will be tracked by the nearest cell tower.
In America, we do have the right to peaceful protest. These steps will help make sure that your phone is not unjustly used against you by law enforcement. Please know the law, and keep yourself safe.
You bought a new router.....now what?
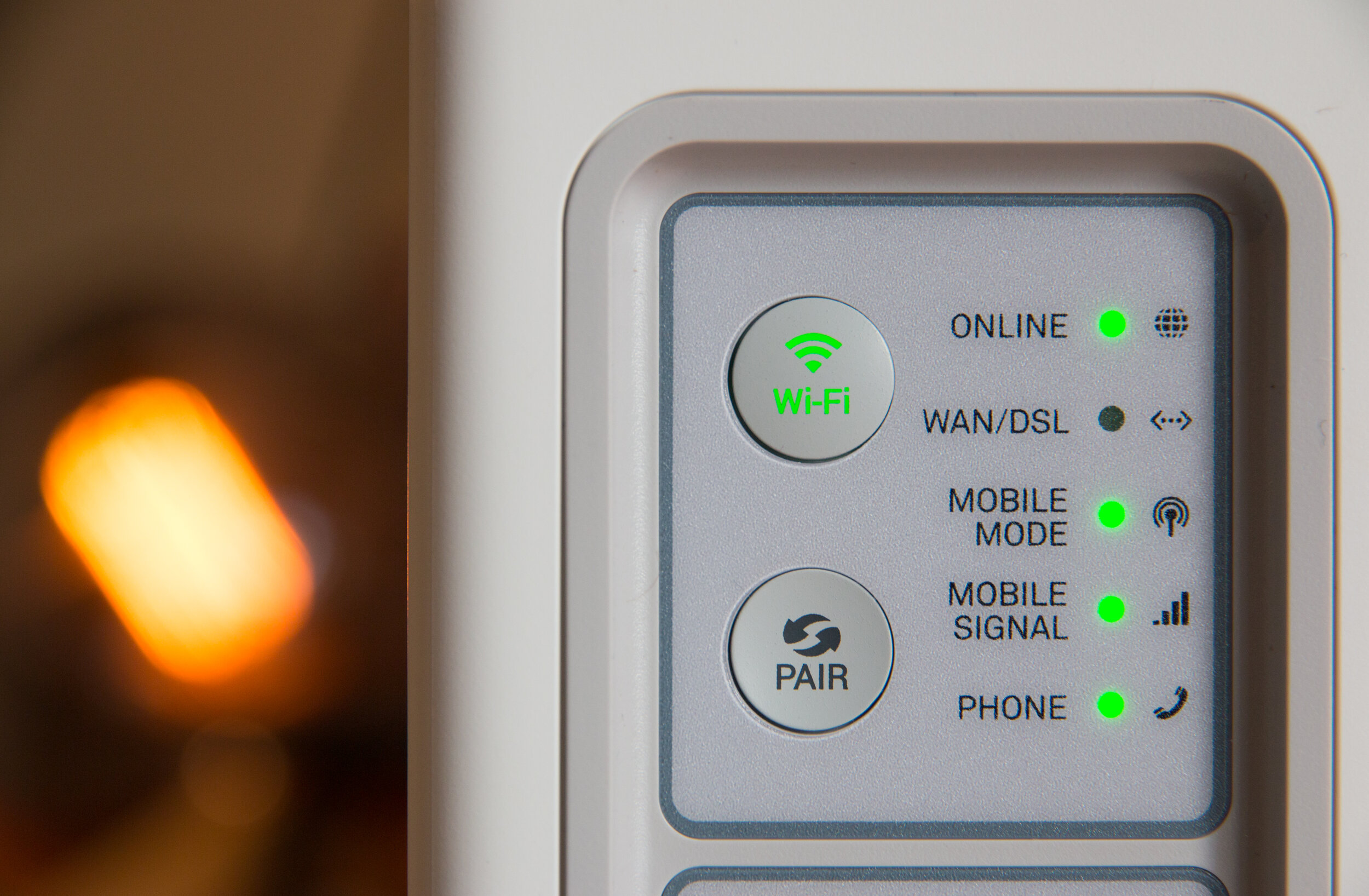
Steps to better secure your router
Routers nowadays are plug and play right out of the box. But unfortunately, securing a router is not as simple.
WHY DO YOU NEED TO SECURE ? WHATS THE RISK?
Leaving your router unprotected will allow hackers monitor your Wi-Fi transmissions and collect data while you are browsing the internet. Using this data they can get your passwords and other private information.
The good thing is that most routers, will have the WPA2 encryption protocol automatically enabled by default. This adds some security to your routers Wi-Fi network.
Setting up your router
what the F*ck is the difference between WPA/ 2 & WEP
What is WPA/WPA2?
WPA/WPA2 is an encryption protocol to obfuscate your data that is transmitted via Wi-Fi. It replaced WEP, which was the previous protocol that was used for Wi-Fi encryption and was found to be easily cracked by most modern computers .
If I am scanning your Wi-Fi with my computer and you are using WEP, I can eventually discover your router's password. From there, I can start just collecting all the browsing data that you are doing on your computers. WPA/2 is a better encryption protocol making it harder for me to decrypt your password.
Even though by default routers have this new protocol enabled, your router has other points of access that hackers can use to gain entry. Below are the steps I taker to set up a router securely.
1. Connect your computer directly to your router via an ethernet cable, then navigate to the router management web page that is mentioned in the booklet that comes with the router. Use the username and password to access the site.
If you lost the booklet, you can type your IP address into your web browser, and then change the last number to 1 to access the page. Here is an example link: 192.168.0.1
Below is a how-to geek article on how to find your IP address.
2. The next thing I do is change the admin’s page default password, because there is malware that will use a default password list to break into a router. There are also web sites that have a list of default passwords.
You can change this in the settings page alongside the username to be extra safe.
3. I then change the Wi-Fi name and password since the name tells the model of the router, making it easier for hackers to find malware.
Make your new password at least 12 characters or more and something that you can remember.
If you are super paranoid, you can enable a guest network and give that to people who visit. There usually is an option to isolate this network.
4. Next, I check that WPA2 is actually enabled. For the encryption type pick WPA2 Personal + AES (CCMP).
5. Finally, I check that the firmware of the router is up to date in the settings. Updating prevents most malware from affecting your router
In your admin dashboard, there will be an option in the settings page to do this automatically, but you can also check for updates on the routers company support page.
After this, the router resets, you are done. Once you do these steps, then you have a hardened your home network from them, dastardly hackers. While you won't be 100% protected, it will make you less of a target than other open Wi-Fi networks.